Going SIEM-less: The SMB Cybersecurity Guide for 2026
Your SIEM was supposed to give you visibility. Instead, it gave you 10,000 alerts a day, a six-figure invoice, and a backlog your team will never clear. For a lot of SMBs, that's where the SIEM story ends: not with a security breach, but with a quiet decision to stop pretending the tool is working.
That's what "going SIEM-less" actually looks like in practice. Not a radical architectural overhaul, but a practical reckoning with the gap between what SIEMs promise and what lean security teams can realistically operate.
Why You Might Need a SIEM Alternative
Traditionally, companies turn to a SIEM to gain centralized visibility across their infrastructure. SIEMs collect and aggregate log data from firewalls, switches, endpoints, and other devices spread across an organization’s network. They then use that information to log, identify, categorize, and analyze security incidents and other network events.
In other words, the primary advantage of a SIEM is its ability to bring together data from different sources across the network and correlate events.
The theory is that sometimes it takes the whole network picture to identify a potential problem, and SIEM platforms are designed to provide that perspective. But in practice, many organizations encounter the same three challenges, and according to analysis of a recent Forbes CISO survey, those challenges prompted 44% of organizations to plan to replace their SIEMs in 2025.
Alert Overload
SIEM tools create an extraordinary amount of noise, especially if not properly configured.
Research published in Security Info Watch last year revealed that 14% of security teams claim to receive more than 10,000 alerts daily, while 4% get in excess of 100,000. Even in larger organizations with a dedicated security team, alert fatigue is inevitable.
Part of the problem is that many of these alerts lack the context necessary for security teams to easily distinguish between a genuine incident and a false positive. AI is beginning to change the game here, but it’s not perfect, and the time and effort required for this level of analysis is simply untenable. This problem is particularly dangerous for small and midsize organizations with lean teams and little to no expertise.
Exorbitant Costs
SIEMs have always been expensive, especially for SMBs with limited cybersecurity resources. A study published in CPO magazine in 2021 revealed that 43% of security practitioners believed they were overpaying for their SIEM relative to its capabilities and value delivered. Unfortunately, little has changed.
Cloud adoption has sent SIEM costs into the stratosphere. Data volumes have skyrocketed, and SIEM’s outdated per-gigabyte pricing models have driven costs higher than even the largest businesses can afford. For SMBs, this creates a painful irony: the more your network grows, the more your security costs escalate, even if your risk profile stays the same.
Complexity, Integration Challenges, and Tool Sprawl
SIEM solutions can also be extremely difficult to implement and manage. Network and security teams must commit to significant and ongoing manual configuration, integration, and maintenance efforts for a SIEM tool to be effective.
Even then, as the volume of data increases, scalability can become an issue. Query response times increase, routine incident response tasks become a burden, and legitimate threats get ignored.
For many SMBs, the real problem isn’t just the SIEM itself. It’s the tool sprawl that surrounds it. A SIEM typically requires a constellation of log sources, integrations, and supporting tools to function as intended. Managing all of that is a full-time job, and most lean IT teams simply don’t have the bandwidth.
Why NDR Is the Best SIEM Alternative for SMBs
Organizations are actively searching for SIEM alternatives to solve their ongoing visibility problem. As it turns out, they’re finding the answer in Network Detection and Response.
Packets don’t lie. Going beyond device logs and getting an independent perspective from the network flows between endpoints can help spot network anomalies that logs would never catch. Combined with the endpoint perspective from an EDR tool, this approach can be an extremely powerful combination.
NDR can be a more complete view. SIEMs work by collecting logs for you to analyze. That’s great, but they’re only capturing data from devices you know about and have configured to report. There are a couple of problems with that:
- What if there are devices you don’t know about? The news is full of stories about Shadow IT, and the best way to capture this traffic is through network flows.
- What if there are devices that can’t send logs or install EDR due to technical limitations? We’re looking at you, IoT and SCADA.
A flow archive can check the same boxes as a SIEM. Another “unique” benefit of SIEMs is that they keep logs and allow you to review data from events that happened in the past, but they can be clunky and slow. Tools like Nomic Insight replace device logs with network flows, making them easy to interrogate, search, and filter. They can serve the same purpose as a SIEM’s logs and provide a user-friendly pivot point for analysts as they review interesting or anomalous behavior.
NDR is SMB-friendly. NDR and SIEM are technically not the same thing, but they can both answer the question of network visibility and anomaly detection. SMBs will find that NDR is most likely the more cost-effective and simpler solution, particularly when it’s bundled with a managed service.
Here’s how NDR and SIEM compare across the dimensions that matter most for SMBs:
Before You Buy a Lightweight SIEM, Consider This
Search for the best SIEM tools for small businesses, and you’ll find plenty of vendors offering what they describe as a “lightweight SIEM.”
These platforms promise easier deployment and lower costs, but they still rely on the same fundamental approach: collect logs, store them, and analyze alerts. That means organizations still need to manage ingestion pipelines, maintain integrations, and investigate large volumes of alerts.
Your SMB cybersecurity team doesn’t need a smaller SIEM. They need to reduce the amount of data and noise they have to process in the first place. For teams already struggling with tool sprawl, simplifying the security architecture is going to offer far more value than adding another tool designed to manage alerts from all the others.
Building Your SIEM-less Stack
If NDR can provide much of the visibility organizations traditionally expect from a SIEM, the next logical question is: what does a SIEM-less security architecture actually look like?
At its core, a SIEM-less architecture means approaching telemetry differently, combining a few focused tools that provide the same coverage as a traditional SIEM with far less complexity. For SMB cybersecurity teams, that stack usually includes three key components.
Endpoint Detection and Response (EDR)
EDR tools provide visibility into activity occurring on managed endpoints, including malware detection, behavioral monitoring, and threat response. This is an important piece of the puzzle: EDR gives security teams deep insight into what’s happening directly on user devices and servers.
However, EDR has limitations. You can only deploy it on systems that support endpoint agents, which means some part of the network may still fall outside your visibility.
Network Detection and Response (NDR)
Network Detection and Response fills that gap. Instead of relying on device logs, NDR analyzes traffic moving between systems across the network. That allows it to detect:
- Lateral movement across devices
- Suspicious communication patterns
- Data exfiltration attempts
- Activity involving unmanaged or unknown devices
Because it observes network traffic directly, NDR can identify behavior that may never appear in device logs. For many organizations, this network perspective is exactly what was missing from their original security stack.
What to Look for in an NDR Vendor
Not all NDR tools are built for SMBs. When evaluating managed NDR vendors, lean security teams should look for a few specific things:
- Passive deployment with no endpoint agents required. This means faster time-to-value and no device compatibility headaches.
- Full coverage of East/West and North/South traffic. East/West is traffic between internal devices. North/South is traffic between your internal network and the internet. You need visibility into both.
- A managed service option. Your team should receive triaged, actionable alerts - not raw telemetry - and a team of experts that can help you interpret the info.
- Flow archives for historical investigation. This is the feature that lets NDR replace the forensic logging function of a traditional SIEM.
That last point is worth emphasizing. One of the most common objections to going SIEM-less is: “What about incident investigation? Don’t we need logs?” The answer is that well-designed NDR flow archives give you significant investigative capability, in a format that is far easier to query and filter than a traditional SIEM’s log store. Tools like Nomic Insight are designed with exactly that use case in mind.
Managed Security Monitoring
Finally, many SMB security teams don’t have the resources to monitor alerts around the clock. A managed service layer helps close that gap by ensuring suspicious activity is investigated quickly and that internal teams receive actionable intelligence rather than raw telemetry.
Together, EDR, NDR, and managed monitoring create a practical, SIEM-less form of threat management that can deliver the same visibility organizations once expected from a SIEM, without the complexity, cost, or operational overhead.
When SIEM-less Works (and When It Doesn’t)
At this point, it’s fair to ask: does every organization need to go SIEM-less?
The honest answer is no. SIEM platforms do still have their place, especially in large enterprise environments with dedicated security operations centers (SOCs) and teams of analysts responsible for managing complex detection pipelines.
In short, a SIEM-less approach tends to work best for organizations that:
- Have small or lean security teams
- Don’t have a dedicated SOC or SIEM engineering resources
- Struggle with alert fatigue from existing tools
- Need visibility into unmanaged, IoT, or legacy devices
- Want to reduce tool sprawl without sacrificing coverage
A note on compliance: SMBs operating under regulatory frameworks like HIPAA, CMMC, or PCI DSS sometimes assume they need a traditional SIEM for audit purposes. In practice, NDR flow archives can satisfy many of the same visibility and logging requirements, often more cleanly than a sprawling SIEM deployment. If your compliance framework requires evidence of network monitoring and incident investigation capability, a well-documented NDR solution paired with a managed SOC is a defensible and often preferable alternative to a full SIEM build-out.
But for organizations that operate large SOCs, require extensive log retention for complex regulatory environments, or manage highly intricate infrastructures, a SIEM might be the more sensible option. Crucially, those environments typically only exist in large enterprises.
Nomic’s SIEM-less Alternative
A combination of EDR and managed NDR can help organizations that can’t realistically deploy or manage a traditional SIEM within their environments.
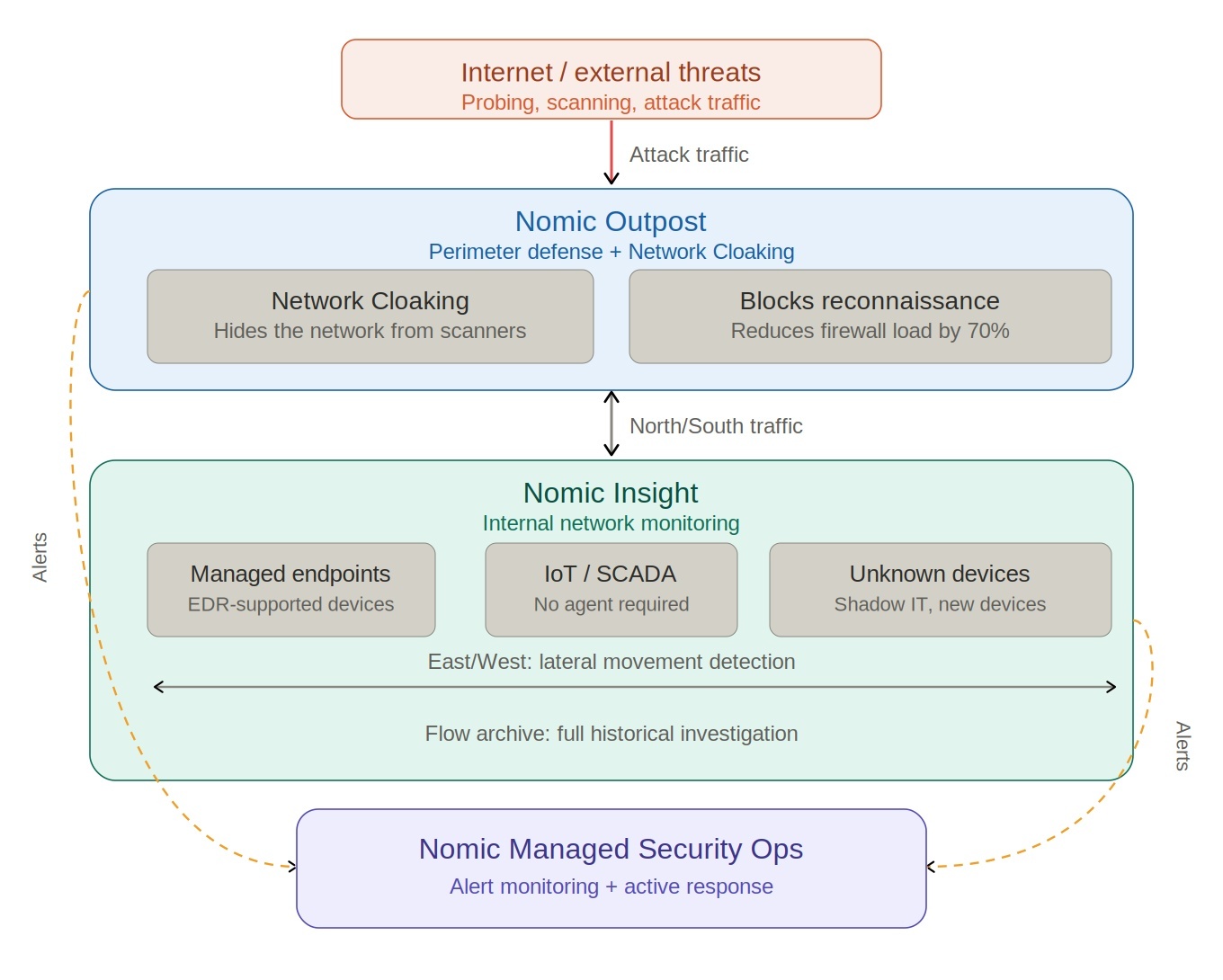
At Nomic, we provide a solution built specifically around that idea.
Nomic Outpost helps customers hide their perimeter by preventing attackers from conducting reconnaissance and identifying misconfigurations that malicious actors could use to gain access to the network. By blocking this activity early, Outpost also helps reduce inbound traffic by 70% and cut down the volume of unnecessary traffic reaching internal systems. That effectively reduces your public attack surface to zero.
Nomic Insight provides a broader network view, analyzing East/West traffic between devices and North/South external communications. Insight uses network flows to detect anomalies and suspicious behavior across the entire network, including areas EDR might miss, such as unmanaged devices or lateral movement.
Together, these capabilities give security teams richer context and a more complete understanding of potential threats, without the complexity, cost, and operational burden of traditional SIEM platforms.
With this visibility, teams can quickly:
- Identify infected devices
- Fix misconfigurations
- Prioritize vulnerabilities for remediation
Insight also maintains historical network visibility, helping organizations investigate past activity while reducing the load placed on traditional logging systems.
Nomic pairs these capabilities with a 24/7 security team that assists with monitoring, research, and troubleshooting. The result is a practical SIEM-less threat management solution that allows SMB cybersecurity teams to gain full network visibility while keeping their environments simple and easy to manage.
Ready to see what a SIEM-less architecture looks like for your organization? Contact our team or explore Nomic Insight to get started.


Ted has worked with network security and web technologies for almost 30 years, beginning his career as a full-stack web engineer and transitioning to network security. He now guides Nomic and its supporting initiatives, including CINS Active Threat Intelligence.